Cybersecurity: Digital resilience for your business
In a digital world, cybersecurity is not just a nice-to-have, but a matter of survival. We support you in developing robust security strategies for the cloud, IAM and governance – with a focus on safeguarding your value creation in the long term.
Digital transformation makes businesses more vulnerable, but also more reliant on secure systems
Effective cybersecurity requires more than just technical solutions – it needs to be strategically integrated into business processes, with clear lines of responsibility and a firm commitment to protecting valuable assets.
Cyberattacks are becoming increasingly complex and frequent – even for small and medium-sized enterprises. At the same time, there is a shortage of qualified security professionals, which makes it difficult to build up in-house expertise. Added to this are rising regulatory requirements such as the GDPR and the NIS2 Directive, which oblige companies to implement proactive security management.
Cybersecurity is not just an IT issue, but a key component in ensuring the long-term viability of any business.
Our approach: The cybersecurity process model
We structure our approach around a holistic process model that covers all phases of security management – underpinned by end-to-end governance.

-
Governance forms the backbone of our cybersecurity strategy and underpins every stage of security management. A clearly defined governance framework ensures that security policies are implemented in compliance with regulations, resources are allocated optimally, and risks are continuously assessed. Only in this way can security be effective and adapt to evolving threats in real time.
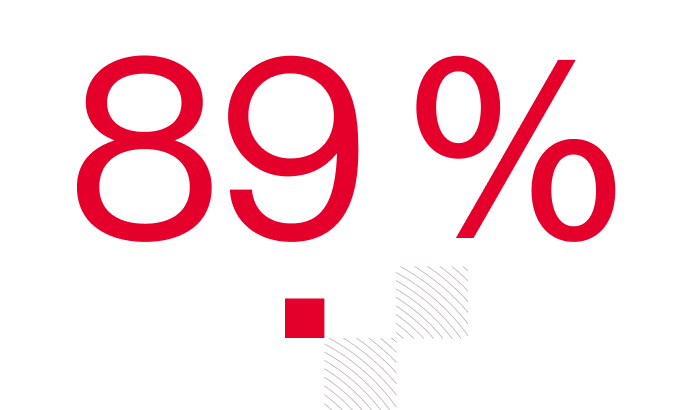
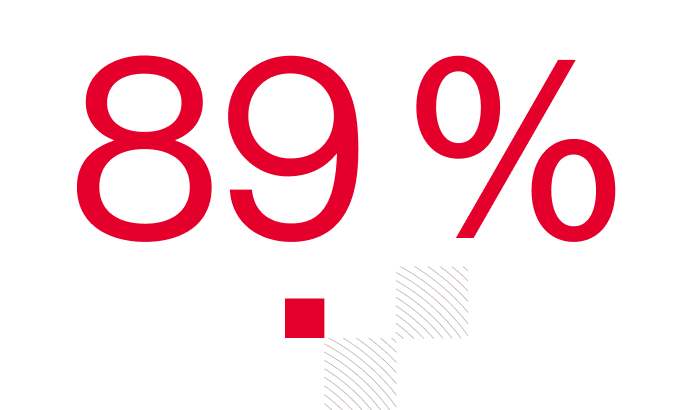
According to PwC, 89 per cent of German companies have been affected by cyberattacks over the past three years, despite the fact that investment in IT security is on the rise in this country. Why aren’t these efforts paying off? One key reason is that traditional security strategies neglect human-computer interaction. Human-centred security addresses precisely this issue and puts people at the heart of the process.

A field of the future: Cybersecurity for AI
AI systems are both new targets for attack and powerful tools for defence. We develop strategies to integrate AI applications securely and protect them from manipulation. Our work is structured around three key pillars:
Use AI to Secure IT
- Targeted use of AI to strengthen defensive security capabilities
- Including intelligent security monitoring, automated threat detection and AI-based log analysis
- Example: Our solution detects anomalies in real time and automatically prioritises critical security incidents.
Secure AI Operation
- Security and trust as the foundation for the responsible use of AI systems
- This includes the implementation of AI architectures, ranging from identity and access control to monitoring and compliant operating models.
- Example: We develop governance frameworks for the use of AI models in corporate environments.
Use AI to Attack IT
- Understand how attackers use AI to specifically strengthen their own defences.
- This includes researching AI-powered attack methods, such as automated penetration tests and social engineering attacks, in order to proactively develop defensive measures..
- Example: Our test simulations help companies harden their systems against advanced attacks.

The benefits you gain from the right cybersecurity strategy:
- Risk minimisation: Avoid costly data breaches and system outages.
- Innovation security: Enable the responsible use of new technologies such as generative or agent-based AI.
- Scalability: Flexibly adapt security measures to your business growth.
Contact our cybersecurity experts and protect your business proactively and with a view to the future.